
The world today is interconnected with innumerable applications and identities. Likewise, the digital environment in the workplace has also extended significantly. Access management is a solution that enables seamless access to applications while ensuring risk factors are controlled.
Access management is an irreplaceable tool in the current covid influenced business landscape. It makes a vast difference to user experience, productivity, and security from the first time a user accesses an application. Some essential modules of access management are single sign-on, authentication capabilities that might include multifactor authentication(MFA) or Passwordless authentication, and some adaptive access control functionalities.
 Let’s assume in an organization there are 500 employees and each employee has access to an average of 40 applications. Ideally, in order to maintain optimum security levels, each employee would have to log in and authenticate themselves every time they use any application. But, not only is it a tedious process but a large security loophole. Most applications rely on passwords for login, but with the need to have a unique password, it isn’t humanly possible to have a different password for each application.
Let’s assume in an organization there are 500 employees and each employee has access to an average of 40 applications. Ideally, in order to maintain optimum security levels, each employee would have to log in and authenticate themselves every time they use any application. But, not only is it a tedious process but a large security loophole. Most applications rely on passwords for login, but with the need to have a unique password, it isn’t humanly possible to have a different password for each application.
This leads to password fatigue and users resort to noting down passwords in excel sheets, notepads, sticky notes, books, saving passwords in their browser, and more. Some might just reuse the same password with minor tweaks that are almost too easy to hack into.
The foolproof method to protect applications, user accesses without compromising on security or productivity is Single Sign-On (SSO). With SSO, the admin predefines the applications that will come under this solution, and with a single login, the users can now access all their applications. The applications could be SAML or web-based and the right SSO solution will be able to provide login to all the applications without any hassle.
Another important dimension of Access Management is authentication. Password management greatly helps in this direction. A password manager helps store all the passwords of the applications. It also helps by providing self–service password capabilities such as password reset and account unlock.
These tools drastically change the way IT time is utilized as well. With SSO and password management, users don’t have to constantly rely on helpdesk assistance. This frees their time for more crucial tasks as well.
However, logging in with a single credential to all the applications can come with its own set of risks. Thus, password management solutions are also equipped with multi-factor authentication (MFA) capabilities. MFA deals with authenticating the user with some predefined factors.
There are 6 factors of authentication:
- What you know – passwords
- Who you are – biometric data
- What you have – OTP
- What you do – keystroke
- Where you are – IT address
- When you act – time frame
These factors of authentication are programmed for each application in a way as to curb any possibility of a security breach. Depending on the sensitivity of the application, 2-factor or more factors can be predefined. These ensure that even if a hacker gets through the first layer such as a password, they will fail to login when a second factor like biometric is asked.
These tools transform the way security is perceived. However, sometimes solutions have to adapt to the circumstances. What if a user is trying to login into a particular application multiple times because they may or may not be the right user? The multiple attempts are a clear warning of outside user access.
In such times, adaptive authentication mechanisms provide even more efficient security. Adaptive authentication relies on the context behind each access. For example, if a person working out of San Francisco suddenly tries to login in from Switzerland, that is a clear indication of a red flag. The same is the case if the IP address of a user is constantly changing or if a user is trying to access a sensitive application at a different time than usual?
All these attributes individually or put together could help decipher whether access is safe or not. If the access is deemed not safe, then the authentication levels to gain the trust are elevated or the login attempt is blocked altogether.
To combat today’s digital threats, a proactive approach to security is the way forward. Security models like zero trust enable this possibility. However, it can be a cumbersome task when it isn’t implemented appropriately. Authentication multiple times over different applications using passwords can be a hassled approach that leads to users taking the shortcut way by reusing passwords, using them with minor tweaks, and so on.
Passwordless Authentication can ensure this doesn’t happen! Passwordless authentication makes authentication possible with zero factors! A user’s face, voice, fingerprint, and so on and captured seamlessly in an app. These are all supported with powerful and secure blockchain technology. These biometrics are then associated with their corporate credentials, which enables them to authenticate using their biometrics instead of their username and password. This method takes authentication one step forward by eliminating MFA and ensuring the highest level of user experience.
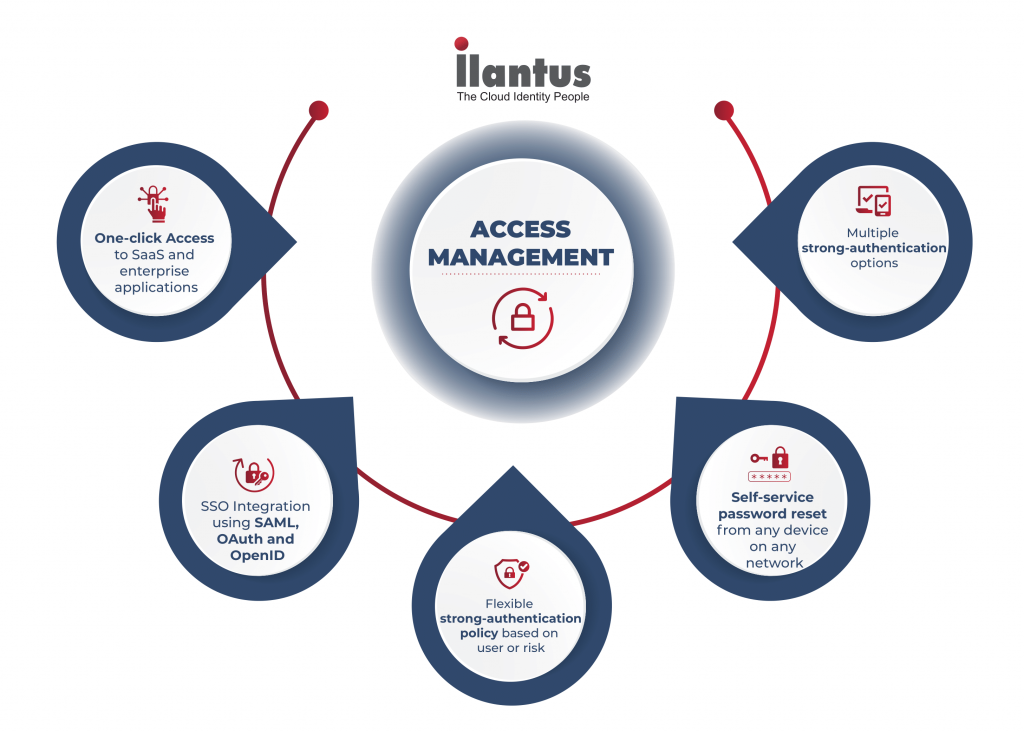
Ilantus access management solutions enable users with all these capabilities and more. When access management is brought together with identity governance and administration, organizations can obtain a holistic IAM solution.
Access management can help secure access and provide users with a seamless experience. Identity Governance and Administration can help monitor these accesses and the different processes behind acquiring them. Learn more about Ilantus’ Converged IAM approach here!
